Mobile financial systems have made transactions faster and more accessible. These tools are now a preferred choice for individuals and businesses looking for payment solutions.
With convenience comes also risks. Cybercriminals continuously look for vulnerabilities to exploit user and business data. This makes mobile security against financial threats a necessity to maintain trust and protect sensitive information.
To secure the entire ecosystem, all levels must be protected. From user devices to payment systems, proactive measures help address mobile security financial threats & solutions, ensuring smooth and safe financial operations.
This blog covers the security threats in mobile finance apps and offers practical measures to address them. It highlights key risks and solutions for users, devices, and service providers.
Common user threats in mobile wallet applications
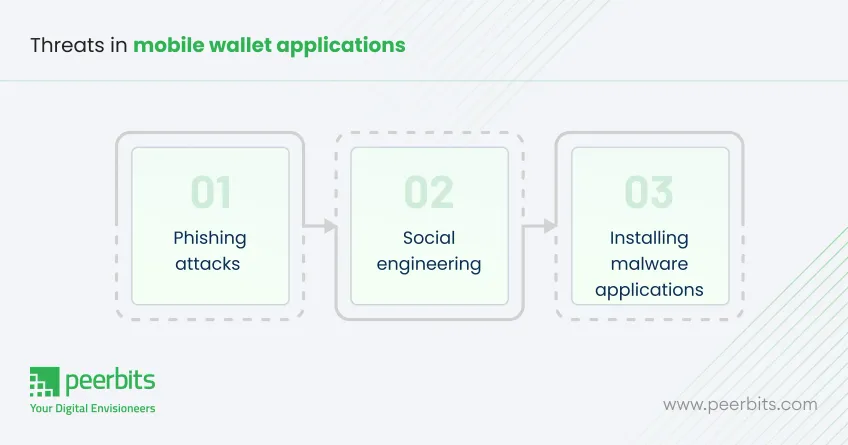
Mobile wallet applications come with potential risks for users. Being aware of common threats like phishing, social engineering, and malware helps individuals protect their sensitive information and financial assets. Let’s understand these threats in detail:
1. Phishing attacks
Phishing is the most common threat where attackers exploit users through fraudulent communications. These deceptive messages, often appearing legitimate, trick users into providing sensitive information like passwords or credit card details.
Possible security measures:
- Educate users on recognizing phishing emails and messages.
- Encourage checking URLs and verifying communication sources.
- Use email filtering tools to block fraudulent messages.
2. Social engineering
Social engineering involves manipulating users into revealing confidential information. Attackers often pose as trusted figures or create a sense of urgency to coerce users into disclosing login credentials or financial details.
Possible security measures:
- Promote awareness of common social engineering tactics.
- Advise users not to share personal information over the phone or online without verification.
- Implement multi-factor authentication to provide an additional layer of security.
3. Installing malware apps
Users may unknowingly install malicious apps disguised as legitimate ones. These apps can steal personal data, monitor user activity, or even perform unauthorized transactions, putting users' financial information at risk.
Possible security measures:
- Encourage users to only download apps from trusted app stores (e.g., Google Play, Apple App Store).
- Use mobile security software to scan for hidden spy apps and other potential threats.
- Keep devices and apps updated to protect against known vulnerabilities.
Risks associated with mobile devices in financial transactions
Mobile devices have revolutionized financial transactions but come with inherent risks. From data breaches to malware attacks, understanding these vulnerabilities is crucial to ensuring secure operations. Here are a few mobile device-related risks that everyone should be aware of:
1. Illegal access to lost or stolen devices
If a mobile device is lost or stolen, unauthorized access to sensitive financial information can lead to significant breaches. Attackers can easily exploit unlocked devices or weak security settings to access personal data and make fraudulent transactions.
Possible security measures:
- Enable device encryption to protect sensitive information.
- Use remote locking features to lock or wipe the device if lost or stolen.
- Set up biometric authentication to prevent unauthorized access.
2. Outdated systems in mobile
Cybercriminals frequently exploit vulnerabilities in mobile devices, such as outdated software or poorly configured security settings. These weaknesses create opportunities for attackers to steal sensitive data or take control of the device for malicious purposes.
Possible security measures:
- Keep the operating system and apps updated to patch vulnerabilities.
- Install mobile security software to detect and block potential threats.
- Use secure Wi-Fi networks to prevent hackers from intercepting data.
3. Weak security configurations
Inadequate security configurations in devices or apps can leave users exposed to cyberattacks. Weak passwords, outdated apps, and improper security settings can all contribute to the vulnerability of mobile devices.
Possible security measures:
- Regularly update security settings and configurations to maintain device security.
- Use strong passwords and implement multi-factor authentication.
- Disable Bluetooth, NFC, and other unnecessary features when not in use to reduce exposure.
Risks associated with mobile applications
Nowadays, mobile apps are the most booming industry. Surely they provide ease of use but they also introduce various security risks to their users. Issues like data breaches, insecure coding practices, and privacy violations can put both users and systems at risk. Here are some major application-level risks in mobile that you should be aware of:
1. Reverse engineering
Cybercriminals often reverse engineer mobile applications to analyze their code and identify vulnerabilities. By understanding the app’s structure and functionality, attackers can exploit weaknesses to bypass security measures, gain unauthorized access to user data, or inject malicious code.
Possible security measures:
- Implement code obfuscation to make the app's code difficult to understand and reverse engineer.
- Use encryption to protect sensitive data stored within the app.
- Regularly update the app to patch vulnerabilities and add new security features.
2. Tampering with the application
Hackers can manipulate mobile applications by using rootkits or other malicious modifications. These alterations can compromise the app’s integrity, letting cybercriminals bypass security protocols, steal sensitive information, or use the app for fraudulent activities.
Possible security measures:
- Integrate anti-tamper mechanisms to detect and prevent modifications.
- Use root detection techniques to identify if a device has been rooted or jailbroken.
- Employ app integrity checks to verify the app’s code hasn’t been altered.
Taking these measures, mobile financial applications can significantly reduce the risk of exploitation through reverse engineering and tampering.
Merchant-level threats in mobile devices
Mobile devices offer great convenience for merchants, but they also expose them to various security threats. Risks such as fraud, data breaches, and unauthorized access can jeopardize both merchant operations and customer trust. Let’s address some of the major ones here & their possible solutions:
1. Uploading malware on POS systems
Attackers can gain unauthorized access to merchant systems and upload malware on point-of-sale (POS) terminals. This malware can compromise sensitive financial information, such as credit card details, and facilitate fraudulent transactions.
Possible security measures:
- Regularly update and patch POS software to protect against known vulnerabilities.
- Conduct security audits to identify and fix potential weaknesses in the system.
- Install anti-malware software to detect and block malicious activity.
2. Man-in-the-middle (MiTM) attacks on POS and servers
In a Man-in-the-middle (MiTM) attack, cybercriminals intercept communication between POS systems and servers. This allows attackers to capture sensitive payment data, alter transactions, or inject malicious commands without the knowledge of either the merchant or the customer.
Possible security measures:
- Use encrypted communication protocols such as SSL/TLS to secure data transmission.
- Implement VPNs (Virtual Private Networks) to create secure connections between POS systems and servers.
- Ensure server-side validation to verify the authenticity of received data.
3. Relay attacks on NFC-enabled POS systems
Relay attacks exploit vulnerabilities in NFC-enabled POS systems, where attackers use proxy devices to intercept and relay communication between the card and the POS terminal. This allows unauthorized access to payment information and can lead to fraudulent transactions.
Possible security measures:
- Use proximity-based security measures, such as requiring a secure PIN or biometric authentication for transactions.
- Implement NFC encryption to protect transmitted data.
- Ensure POS terminal authentication to confirm legitimate communication between the card and the terminal.
These security measures help protect merchants from threats such as malware, MiTM attacks, and relay attacks, ensuring secure transactions and safeguarding customer data.
Payment service provider (PSP) vulnerabilities
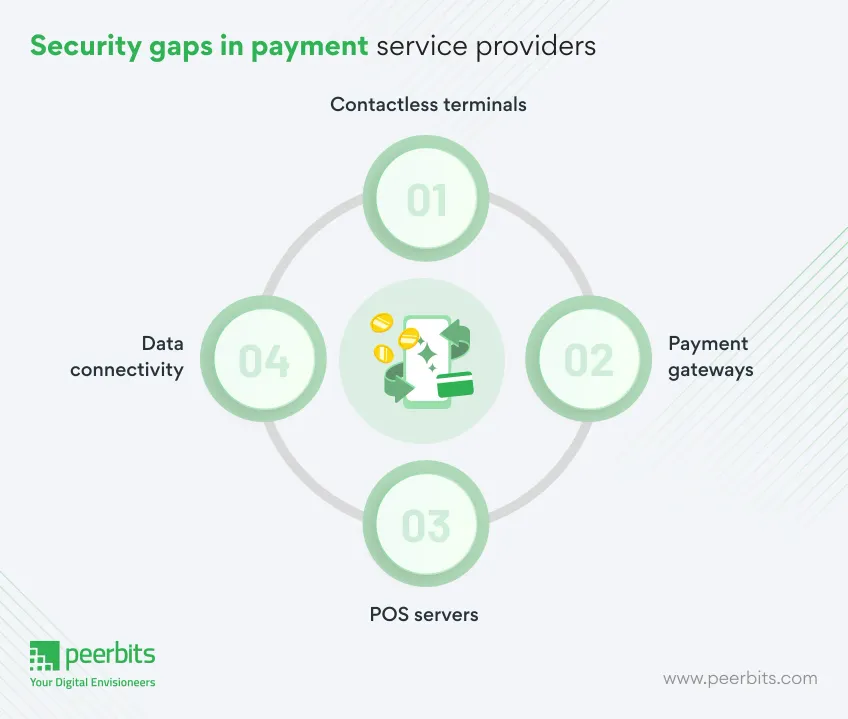
Payment service provider (PSP) vulnerabilities can put the entire transaction process at risk. From insecure payment gateways to compromised software on POS servers, these threats can lead to data breaches and disrupted services.
1. Compromise of software on contactless terminals
Cybercriminals can exploit weaknesses in poorly secured software on contactless payment terminals. Gaining control over these terminals, attackers can intercept payment data or even tamper with transaction processing, leading to data theft or fraudulent activities.
Possible security measures:
- Implement strong access control mechanisms and encryption for terminal software.
- Regularly update software to patch known vulnerabilities and prevent exploitation.
- Conduct security audits and vulnerability assessments on all terminal systems.
2. Compromising payment gateways
Payment gateways are the backbone of transaction processing, and if compromised, attackers can redirect or manipulate payments, steal financial data, or disturb business operations. This type of attack can have severe consequences for both merchants and customers.
Possible security measures:
- Use multi-factor authentication (MFA) for gateway access and ensure secure coding practices.
- Secure gateway communication with TLS/SSL encryption.
- Implement intrusion detection systems (IDS) to monitor for suspicious activity.
3. Software vulnerabilities on POS servers
POS servers are crucial for processing transactions, but if they have unpatched software vulnerabilities, attackers can breach the system. Once compromised, hackers can access sensitive data, including customer payment details, which can lead to data theft or financial loss.
Possible security measures:
- Regularly update and patch software to prevent exploitation of known vulnerabilities.
- Employ network segmentation to limit access to sensitive systems.
- Use firewalls and anti-virus software to protect the POS server.
4. Compromise of data connectivity
Attacks targeting the data connectivity between payment systems, such as between POS terminals and payment gateways, can lead to the interception or modification of transaction data. This exposes payment systems to risks like fraud, data breaches, and unauthorized access.
Possible security measures:
- Use VPNs or private networks to secure communication between terminals, gateways, and servers.
- Encrypt transaction data in transit to prevent unauthorized access.
- Monitor and secure network infrastructure with real-time threat detection tools.
These measures help mitigate PSP vulnerabilities by ensuring layered security, regular updates, and compliance with industry standards like PCI DSS.
Acquirer threat impact on mobile payments
Acquirer threats involve risks to payment processing systems, where attackers target the infrastructure behind transactions. These threats include malware, rootkits, and attacks that disrupt the integrity of payment systems.
1. Compromise of payment processing systems
If an acquirer’s payment processing system is compromised, attackers can manipulate transactions or launch denial-of-service attacks. This can disrupt payment processing, leading to financial losses and a damaged reputation for businesses involved.
Possible security measures:
- Implement multi-layered security protocols such as end-to-end encryption and tokenization.
- Use intrusion prevention systems (IPS) and real-time monitoring to detect unauthorized activities.
- Establish redundant systems to ensure uninterrupted transaction processing in case of system failure.
2. Malware and rootkits installation
Cybercriminals can install malware or rootkits on acquirer systems to maintain persistent access. These threats are difficult to detect and can exfiltrate sensitive data or disrupt system operations over an extended period, making them highly dangerous for the acquirer and its clients.
Possible security measures:
- Install advanced malware detection software and regularly update it to identify and neutralize threats.
- Use rootkit detection tools to scan and remove any malicious software from systems.
- Enforce strict access controls and least privilege policies to limit potential entry points for attackers.
3. Compromise of data connectivity
Attacks on the data connectivity between acquirers and their payment infrastructure can result in the loss of data integrity or availability. A breach in this communication channel could lead to fraudulent transactions, data breaches, and severe operational impacts.
Possible security measures:
- Secure communication channels with encrypted VPNs and secure socket layer (SSL) protocols.
- Implement network segmentation to isolate critical systems and prevent lateral movement by attackers.
- Regularly audit and monitor network traffic for any signs of unusual activity or vulnerabilities.
4. Repudiating the authority of mobile payment systems
This type of attack undermines the trust in mobile payment systems by challenging the authenticity or legitimacy of transactions. Disrupting the trust in the system can affect both consumer confidence and the operational efficiency of the acquirer.
Possible security measures:
- Ensure secure authentication and digital signatures for transaction verification.
- Use blockchain or distributed ledger technologies (DLT) to provide an immutable record of transactions.
- Invest in reputation management to maintain consumer trust in the payment system.
These security measures focus on enhancing protection at multiple levels within the acquirer’s infrastructure, ensuring the integrity and availability of payment processing while minimizing the risk of manipulation or disruption.
Innovations in mobile finance security
Mobile finance security has seen significant advancements to tackle evolving cyber threats. Key innovations include:
- AI-powered fraud detection: AI and machine learning analyze data in real-time to detect and prevent fraud by recognizing suspicious patterns.
- Biometric authentication: Fingerprint and facial recognition enhance security by ensuring only authorized users can access financial apps.
- Blockchain technology: Blockchain provides tamper-proof transaction records, increasing security and reducing fraud risk.
- End-to-end encryption and tokenization: These technologies secure data transmission and minimize breach risks by replacing sensitive data with non-sensitive tokens.
- Zero trust security models: This approach continuously verifies all users and devices, ensuring only authenticated entities can access financial systems.
These innovations are strengthening mobile finance security and improving user trust in mobile payment solutions.
Advanced security solutions for mobile finance
Mobile finance security has evolved with advanced technologies to better protect user data and financial transactions. Key solutions include:
-
Mobile financial data encryption solutions: Data encryption ensures that sensitive information remains protected during storage and transmission, making it unreadable to unauthorized users.
-
Biometric authentication in financial apps: Biometric methods such as fingerprint, facial recognition, and voice identification strengthen security by ensuring only authorized users can access mobile finance applications.
-
Latest security technologies for mobile payments: Quantum-resistant algorithms and blockchain integration are emerging technologies that offer enhanced protection against evolving threats, securing mobile payments with unprecedented strength.
These advanced solutions are critical in providing robust protection for mobile finance users and building trust in mobile payment systems.
AI vs traditional security in mobile finance
| Feature | AI-based security | Traditional security |
|---|---|---|
| Threat detection | Real-time analysis of patterns using machine learning algorithms to detect unusual activities. | Relies on predefined rules and signatures to detect known threats. |
| Adaptability | Continuously learns and adapts to new threats. | Limited adaptability to new, unknown threats. |
| Response time | Immediate response to potential threats, enabling real-time protection. | Slower response, often requiring manual intervention. |
| Scalability | Can handle large amounts of data and traffic, scaling as needed. | Limited scalability, especially with large user bases. |
| Data privacy | Analyzes data without compromising privacy through advanced encryption techniques. | Dependent on static encryption methods which may be vulnerable. |
| Efficiency | Can automate repetitive security tasks, reducing human error. | Requires manual oversight, increasing the chance of overlooking threats. |
| Cost | Initial high setup cost, but reduces long-term costs by preventing fraud and breaches. | Lower initial cost, but higher risk of costly breaches and fraud. |
| Compliance | Can assist in maintaining compliance by quickly adjusting to new regulations and threats. | Compliance may require manual updates and revisions, risking delays. |
AI-based security solutions offer a more dynamic and effective approach to safeguarding mobile finance, addressing modern threats with higher efficiency compared to traditional security methods.
Conclusion
The rise of mobile financial solutions has brought new opportunities, but also increased security risks. To protect against these threats, businesses must adopt security measures, including encryption, biometric authentication, and AI-powered fraud detection.
User education plays an important role in preventing security breaches. Teaching users to recognize threats and maintain secure practices can reduce vulnerabilities.
A multi-layered approach to security, combining technology and awareness, is essential for safeguarding mobile financial systems. Businesses and users must work together to ensure a secure, trustworthy environment for mobile finance.